[Rocky] 10. DNS - 권한 위임 구성
카테고리: ROCKY
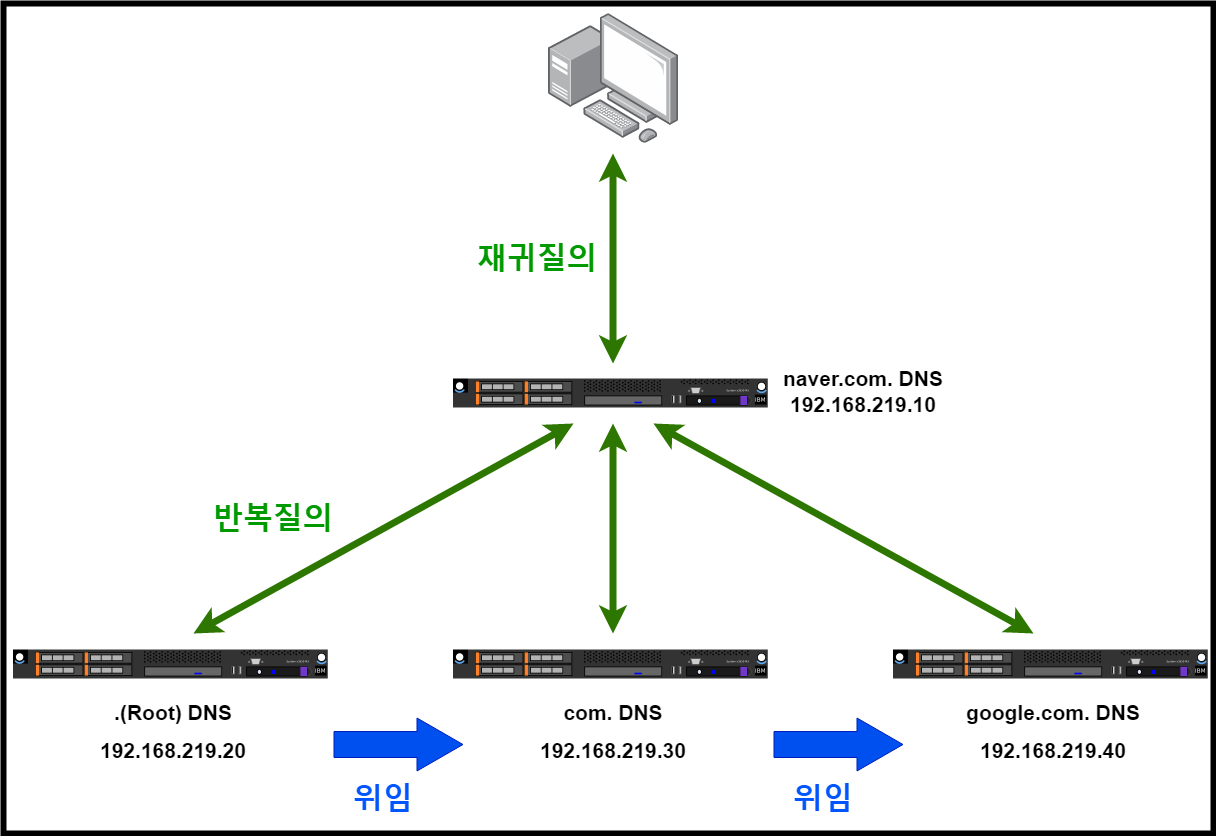
🔔 DNS 권한 위임
상위 도메인에 소속된 하위 도메인에게 해당 도메인의 관리, 서비스 권한을 위임 함(상위 도메인 → 하위 도메인의 NS 레코드 추가, 하위 도메인 → 위임 받은 도메인의 레코드 생성)
-
예시로 www.b2.a2.com. 도메인의 권한 위임
-
.(root) 도메인 : com. 도메인의 NS 레코드 추가
-
com. 도메인 : a2.com. 도메인의 NS 레코드 추가
-
a2.com. 도메인 : b2.a2.com. 도메인의 NS 레코드 추가
-
b2.a2.com. 도메인 : www , host의 A 레코드 추가
-
■ .(root) 네임 서버 구성
■ com. 네임 서버 구성
■ a2.com. 네임 서버 구성
■ b2.a2.com. 네임 서버 구성
🔔 테스트 구성
■ naver.com. DNS 서버 설정
$ vim /etc/named.conf
# 변경
listen-on port 53 { any; };
listen-on-v6 port 53 { any; };
allow-query { any; };
dnssec-enable no;
dnssec-validation no;
$ vim /etc/named.rfc1912.zones
# 추가
zone "naver.com" IN {
type master;
file "naver.com.zone";
};
$ cat /var/named/naver.com.zone
$TTL 86400
@ IN SOA ns.naver.com. root.naver.com. (
2022081001 ;Serial
3600 ;Refresh
1800 ;Retry
604800 ;Expire
86400 ;Minimum TTL
)
IN NS ns.naver.com.
ns IN A 192.168.219.10
www IN A 192.168.219.13
ftp IN A 192.168.219.18
# DNS Root hint 설정
$ cat /var/named/named.ca
~(생략)~
;; ANSWER SECTION:
# 추가
. 518400 IN NS a.root-servers.net.
~(생략)~
;; ADDITIONAL SECTION:
# 추가
a.root-servers.net. 518400 IN A 192.168.219.20
~(생략)~
$ systemctl restart named
# 방화벽 DNS 서비스 허용
$ firewall-cmd --add-service=dns; firewall-cmd --runtime-to-permanent
■ .(root) DNS 서버 설정
$ vim /etc/named.conf
# 변경
listen-on port 53 { any; };
listen-on-v6 port 53 { any; };
allow-query { any; };
dnssec-enable no;
dnssec-validation no;
$ vim /etc/named.rfc1912.zones
# 추가
zone "." IN {
type master;
file "root.zone";
};
$ vim /var/named/root.zone
$TTL 86400
@ IN SOA ns. root. (
2022081001 ;Serial
3600 ;Refresh
1800 ;Retry
604800 ;Expire
86400 ;Minimum TTL
)
IN NS ns.
com IN NS ns.com.
ns IN A 192.168.219.20
ns.com IN A 192.168.219.30
$ systemctl restart named
# 방화벽 DNS 서비스 허용
$ firewall-cmd --add-service=dns; firewall-cmd --runtime-to-permanent
■ com. DNS 서버 설정
$ vim /etc/named.conf
# 변경
listen-on port 53 { any; };
listen-on-v6 port 53 { any; };
allow-query { any; };
dnssec-enable no;
dnssec-validation no;
$ vim /etc/named.rfc1912.zones
# 추가
zone "com" IN {
type master;
file "com.zone";
};
$ vim /var/named/root.zone
$TTL 86400
@ IN SOA ns.com. root.com. (
2022081001 ;Serial
3600 ;Refresh
1800 ;Retry
604800 ;Expire
86400 ;Minimum TTL
)
IN NS ns.com.
google IN NS ns.google.com.
ns IN A 192.168.219.30
ns.google IN A 192.168.219.40
$ systemctl restart named
# 방화벽 DNS 서비스 허용
$ firewall-cmd --add-service=dns; firewall-cmd --runtime-to-permanent
■ google.com. DNS 서버 설정
$ vim /etc/named.conf
# 변경
listen-on port 53 { any; };
listen-on-v6 port 53 { any; };
allow-query { any; };
dnssec-enable no;
dnssec-validation no;
$ vim /etc/named.rfc1912.zones
# 추가
zone "google.com" IN {
type master;
file "google.com.zone";
};
$ vim /var/named/root.zone
$TTL 86400
@ IN SOA ns.google.com. root.google.com. (
2022081001 ;Serial
3600 ;Refresh
1800 ;Retry
604800 ;Expire
86400 ;Minimum TTL
)
IN NS ns.google.com.
ns IN A 192.168.219.40
www IN A 192.168.219.45
ftp IN A 192.168.219.48
$ systemctl restart named
# 방화벽 DNS 서비스 허용
$ firewall-cmd --add-service=dns; firewall-cmd --runtime-to-permanent
■ 결과 확인
$ dig www.google.com @192.168.219.10
; <<>> DiG 9.16.23-RH <<>> www.google.com @192.168.219.10
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 38538
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 1232
; COOKIE: 9e86e8f2c796d2e101000000643f8e7abb50772541ed9edb (good)
;; QUESTION SECTION:
;www.google.com. IN A
;; ANSWER SECTION:
www.google.com. 85045 IN A 192.168.219.45
;; Query time: 0 msec
;; SERVER: 192.168.219.10#53(192.168.219.10)
;; WHEN: Wed Apr 19 15:47:22 KST 2023
;; MSG SIZE rcvd: 87
$ dig www.naver.com @192.168.219.10
; <<>> DiG 9.16.23-RH <<>> www.naver.com @192.168.219.10
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 17135
;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 1232
; COOKIE: ed4211cf7ffbf70101000000643f8ebbf83d38a17073565e (good)
;; QUESTION SECTION:
;www.naver.com. IN A
;; ANSWER SECTION:
www.naver.com. 86400 IN A 192.168.219.13
;; Query time: 0 msec
;; SERVER: 192.168.219.10#53(192.168.219.10)
;; WHEN: Wed Apr 19 15:48:28 KST 2023
;; MSG SIZE rcvd: 86
댓글 남기기